
Install SSL/TLS for Arch Linux Apache Video Guide
Pacman, a package manager written specifically for Arch Linux, is used to install, remove and update software packages. Arch Linux uses a rolling release model, meaning there are no "major releases" of completely new versions of the system.
Pre-requisite commands:-
1: Update the system and install Apache
shell
sudo pacman -Syu
shell
sudo pacman -S apache
2: Start Apache:-
shell
sudo systemctl start httpd
3: Check whether Apache is running:-
shell
sudo systemctl status httpd
4: Create a default SSL directory under the httpd directory:-
shell
sudo mkdir /etc/httpd/conf/ssl
Step 1. Generating a CSR and Private Key with OpenSSL
1: Execute the following command to generate a private key and a CSR -
shell
sudo openssl req -new -newkey rsa:2048 -nodes -keyout /etc/httpd/conf/ssl/server.key -out /etc/httpd/conf/ssl/server.csr
This will create a private key and a CSR with the name of server.key and server.csr respectively; in the default ssl directory.
You will then get a prompt asking you to input the following details regarding your CSR:-
Country Name (2 letter code) [AU]: Type in the 2 letter abbreviation for your country.
State or Province Name (full name) [Some-State]: Full name of the state
Organization Name (eg, company) [Internet Widgits Pty Ltd]:Locality Name (eg, city) []: Complete name of the city, no abbreviations
Organization Name (eg, company) [Internet Widgits Pty Ltd]: If you are a business; Enter your legal entity name. If you're not a business, any value entered will not be used in your certificate.
Organizational Unit Name (eg, section) []: If you are a business; Write the appropriate division of your company. It is best to use something generic such as "IT".
Common Name (e.g. server FQDN or YOUR name) []: Enter your domain name
Email Address []: Enter your email address
After you hit Enter, your Private Key and CSR should be saved successfully in the default ssl directory.
2: To view your CSR, type in the following command:
shell
sudo cat /etc/httpd/conf/ssl/server.csr
You can save the CSR in a .txt file or directly proceed to certificate configuration.
Step 2. Order and Configure the SSL Certificate
The next step in the installation process is to order an SSL Certificate. If you visit our SSL Certificates List page, you will have a number of options available, such as a low-cost domain-validated SSL or a multi-domain SSL.
Cheap SSL Certificates
View our low cost SSL Certificates with domain validation.
Starting at $ per year
Business Certificates
View our Business Certificates to secure and verify your business.
Starting at $ per year
If you require any assistance with selecting an SSL Certificate, please feel free to contact our sales/support team and they will be happy to assist.
1: Order the SSL and complete the checkout process.
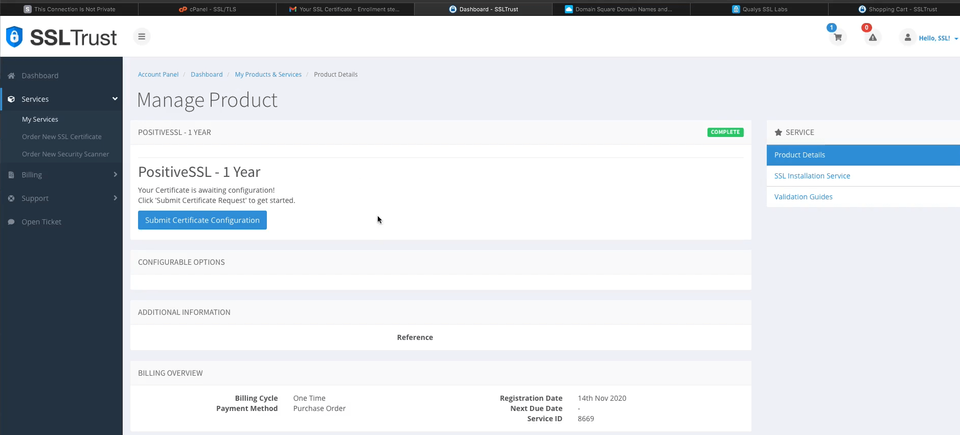
2: Once you have completed the SSL Certificate Purchase you can begin the configuration process. This can be started by going into your SSLTrust account and managing your recent purchase.
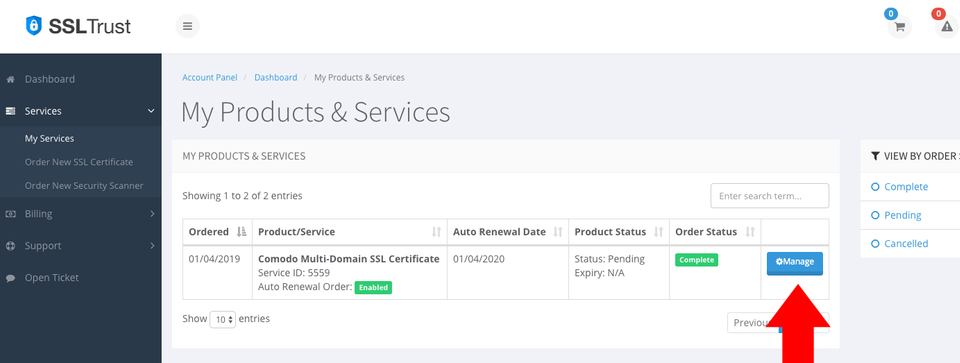
You then will need to click the Submit Configuration button to begin the configuration process.
3: You now need to paste in the CSR you generated using the OpenSSL library in the Ubuntu CLI. This includes the lines:
text
-----BEGIN CERTIFICATE REQUEST---- -----END CERTIFICATE REQUEST-----
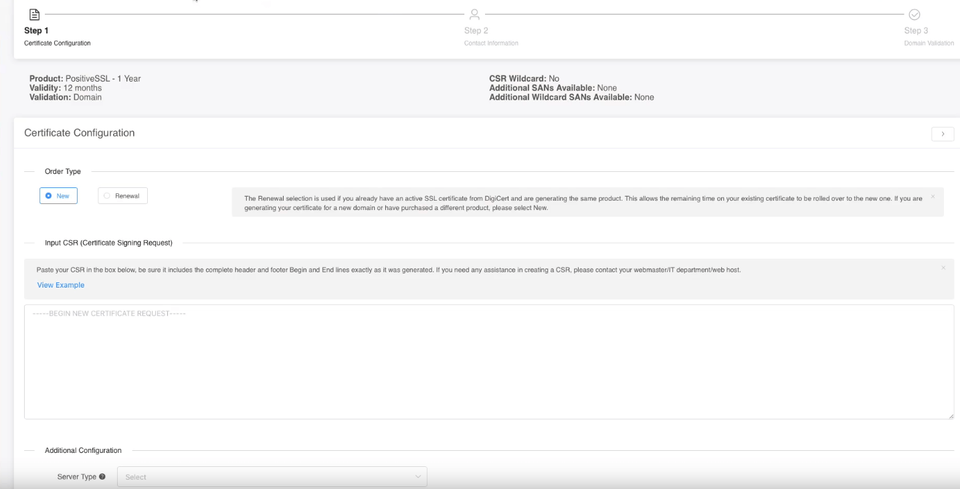
Select Apache/Other for your Web Server Type.
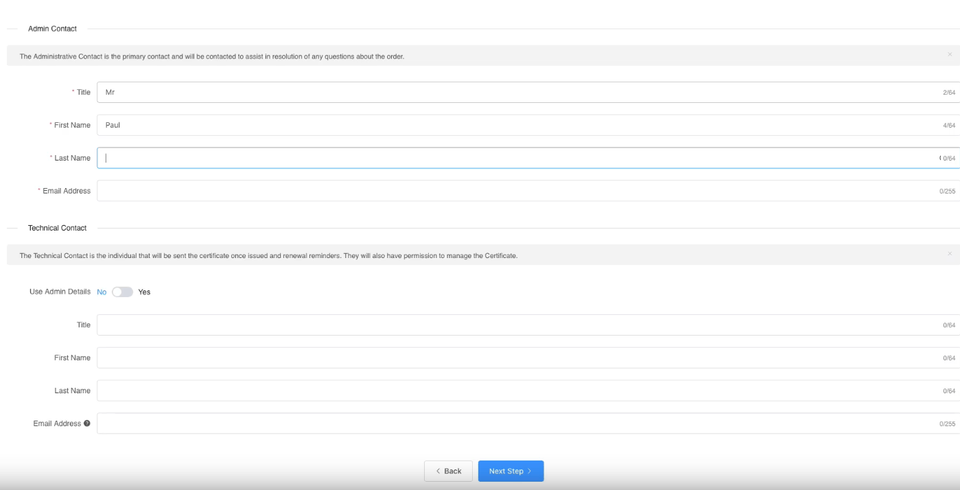
You will need to also enter the Site Administrator Contact Information.
This information is to be of the individual who is responsible to approve and SSL Certificate. If it is a business SSL, it needs to be a contact under the business.
The Technical Contact Information is the details of the individual responsible for the installation and management of the Certificate.
If you have ordered a business SSL, you will also be required to enter your business details. These should be the correct address and phone number and legal entity name. They will be required to be validated by the Certificate Authority, any mistakes will cause delays. More information on Business Validation can be found here.
4: Click Continue to go to the next Step. Here you need to select the Authentication Method to validate your domain name. This is required to prove you own the domain name and have permission to issue an SSL Certificate for the domain.
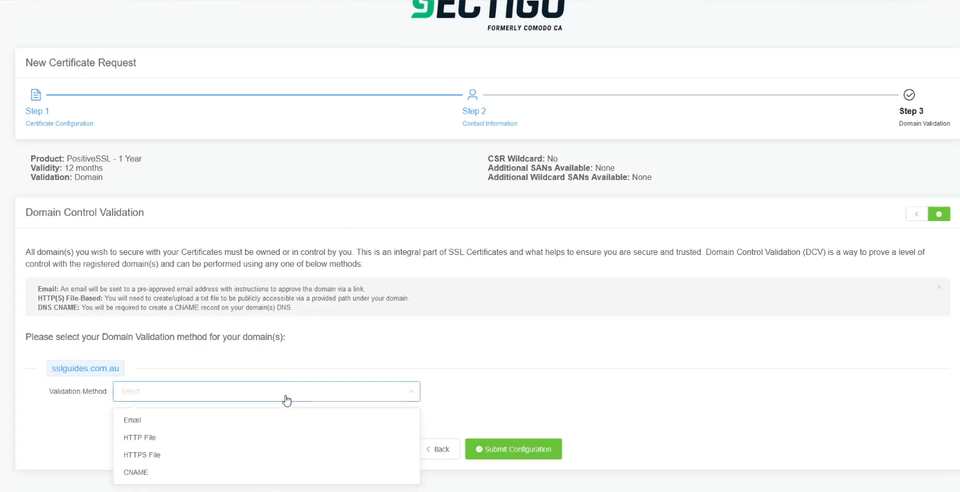
Select the method that will be the easiest for you to use; File-Based Authentication ( HTTP / HTTPS ), CNAME Based Authentication ( DNS ) or Certificate Approver Email.
If you have access to one of the listed emails, this can be the quickest method
Click Continue/Submit to finish the Configuration process.
After you complete the domain validation via your selected method, your SSL will be issued. If you ordered a Business SSL, you will need to wait for the Certificate Authority to complete the Business address and phone validation. If the validation has not progressed, or you have not received your Certificate after some time, please contact our support team so we can check on its status.
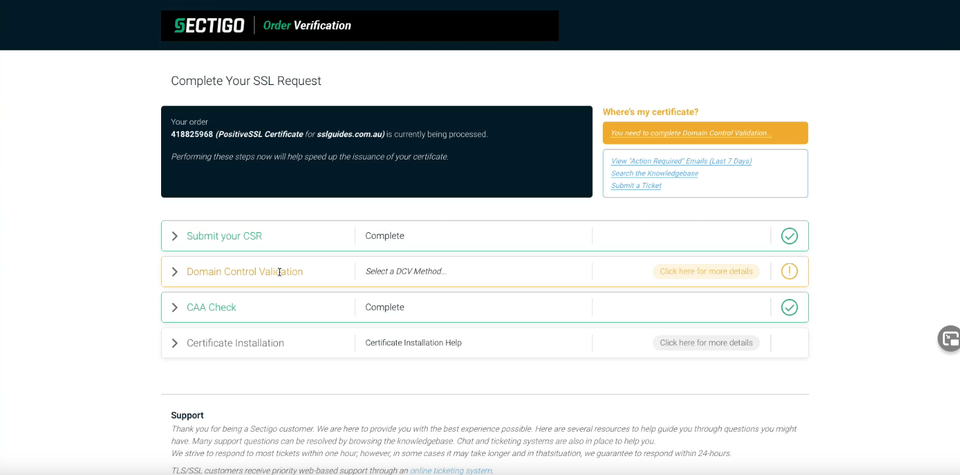
Step 3. Upload the SSL Certificate files to your server
When your SSL Certificate has been issued, you will be emailed the Certificate Directly from the Certificate Authority. You can also download it from your SSLTrust Portal. Downloading it from the SSLTrust Portal is a good option as we format the certificate in an easy to use way.
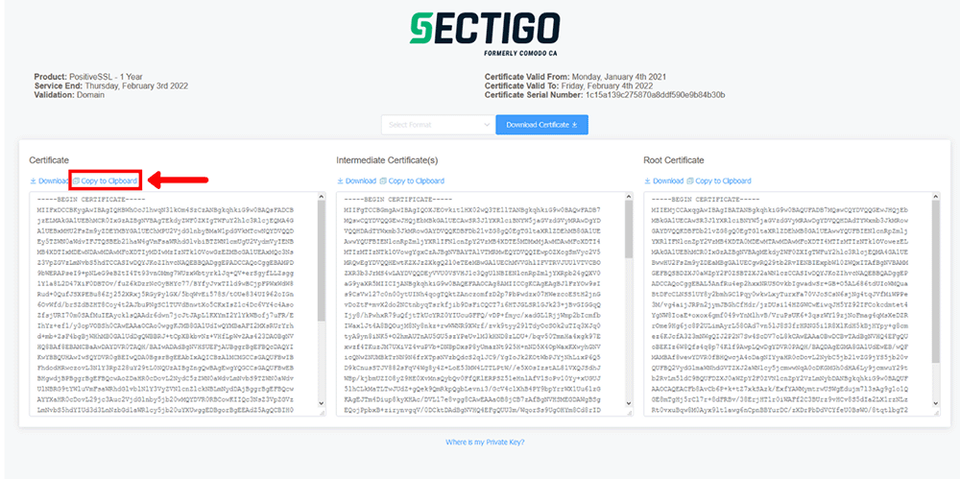
Again; View your certificate management page within SSLTrust
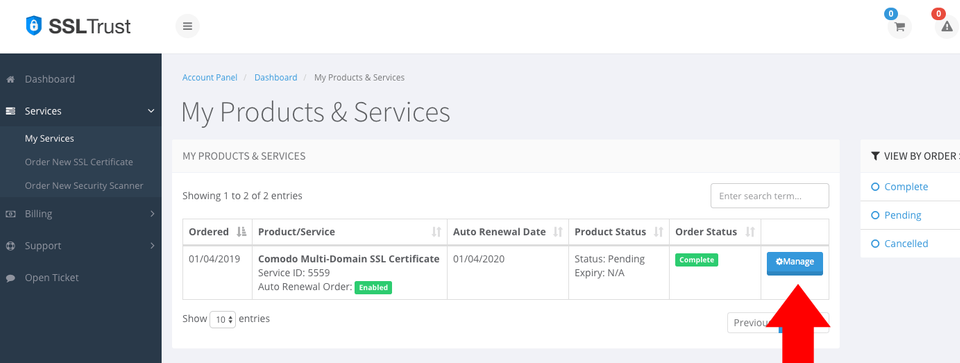
1: Click on the Manage button and collect/download your certificate
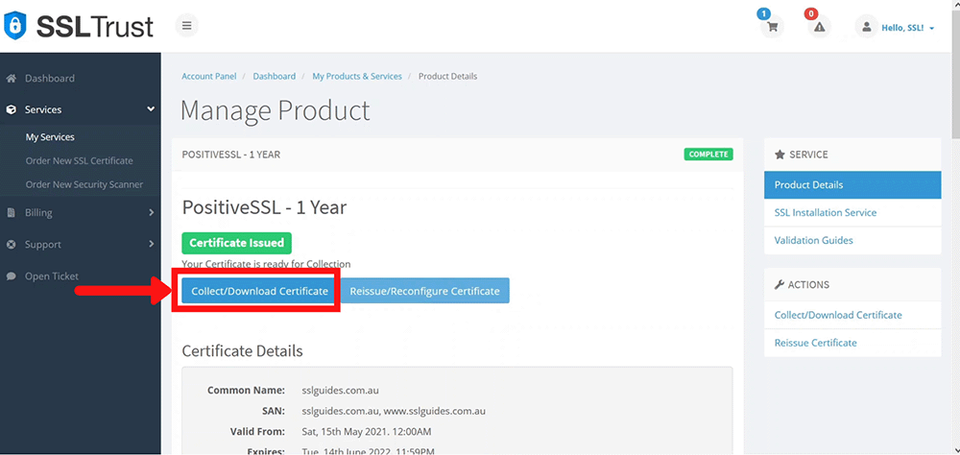
2: Go to the first column and click on copy to clipboard
Now, execute the following command-
shell
sudo nano /etc/httpd/conf/ssl/certificate.crt
Paste your certificate and exit the buffer.
3: Head over to the certificate collection page and click on copy to clipboard on the Intermediate certificate.
Note:- It is recommended that you install your intermediate certificate too so as improve compatibility with browsers; and to minimize the chances of your visitors getting unwanted security warnings on your website.
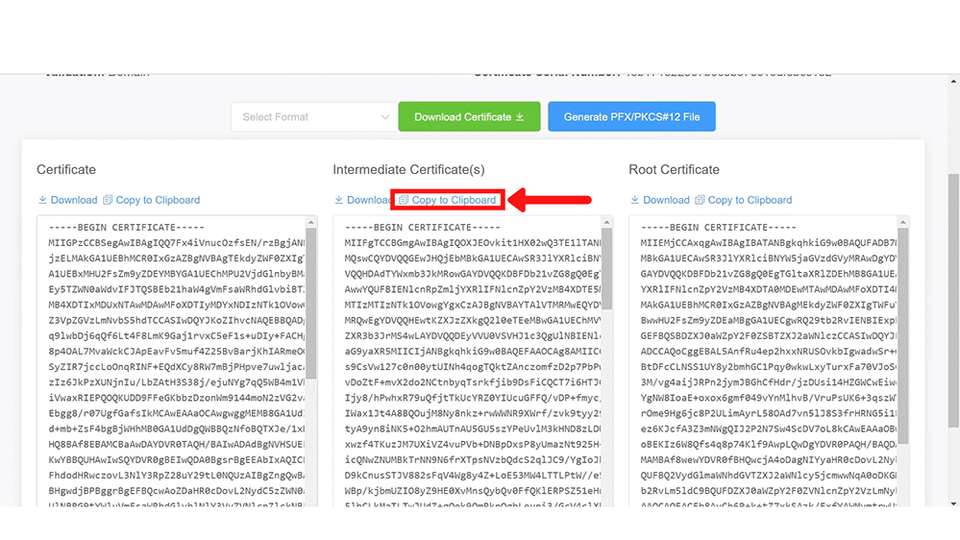
shell
sudo nano /etc/httpd/conf/ssl/intermediate.crt
Paste your Intermediate certificate and exit the buffer.
Step 4. Configure the httpd SSL Parameters
shell
sudo nano /etc/httpd/conf/extra/httpd-ssl.conf
Now edit the secure web server configuration file and locate/modify the directives as shown below.
text
LoadModule ssl_module modules/mod_ssl.so LoadModule socache_shmcb_module modules/mod_socache_shmcb.so Listen 443 SSLCipherSuite HIGH:MEDIUM:!aNULL:!MD5 SSLPassPhraseDialog builtin SSLSessionCache "shmcb:/run/httpd/ssl_scache(512000)" SSLSessionCacheTimeout 300
Save and exit the buffer.
Step 5. Configure the httpd Virtual Host
shell
sudo nano /etc/httpd/conf/httpd.conf
Uncomment the following lines (Remove the '#' symbol):-
text
LoadModule ssl_module modules/mod_ssl.so LoadModule socache_shmcb_module modules/mod_socache_shmcb.so Include conf/extra/httpd-ssl.conf
Additionaly, at the very end, append the 2 following lines:- (Only if you are using multiple virtualhosts)
text
IncludeOptional conf/sites-enabled/*.conf IncludeOptional conf/mods-enabled/*.conf
Furthermore, the most important part of this step is the ServerName and the Certificate location.
Make sure you input the correct certificate path.
text
DocumentRoot "/srv/http"
ServerName yourdomain.com
ServerAdmin you@example.com
ErrorLog "/var/log/httpd/localhost-ssl-error_log"
TransferLog "/var/log/httpd/localhost-ssl-access_log"
SSLEngine on
SSLCertificateFile "/etc/httpd/conf/ssl/certificate.crt"
SSLCertificateKeyFile "/etc/httpd/conf/ssl/server.key"
SSLCertificateChainFile "/etc/httpd/conf/ssl/intermediate.crt"
Also, change yourdomain.com to your domain name.
Then, restart the httpd service
shell
systemctl restart httpd.service
Step 6. Check the SSL is working
SSLTrust's Free SSL Checker is a tool that allows you to test and validate the SSL/TLS certificates installed on websites. Simply enter a domain name and it will analyze the certificate, providing details like the issuer, expiration date, encryption strength, and whether the certificate is properly configured and trusted by major browsers and operating systems. In SSL tests, receiving an "A" rating typically signifies that the SSL certificate and its configuration meet high security standards.
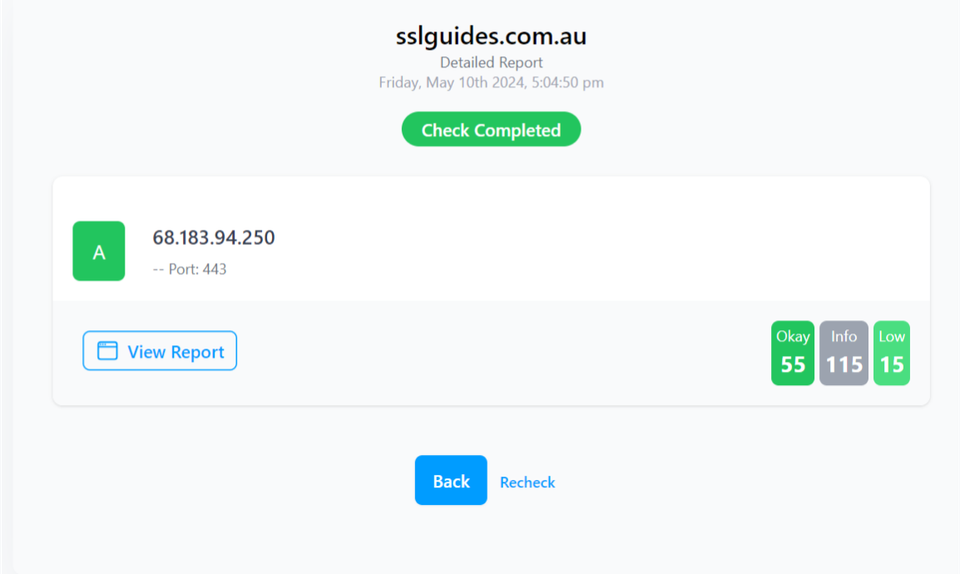
The checker highlights any potential security issues or misconfigurations with the SSL implementation. This free tool makes it easy to verify if a website's SSL certificate is valid and secure, giving visitors confidence their connection is encrypted and their data is protected from eavesdroppers.
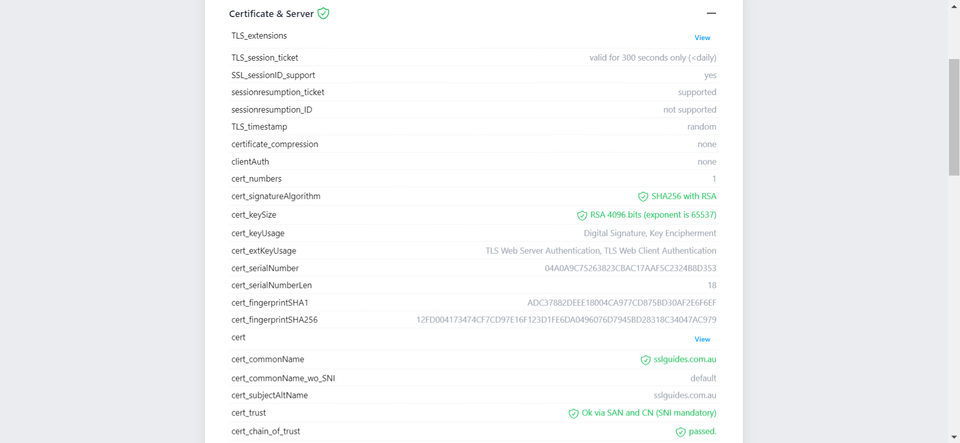
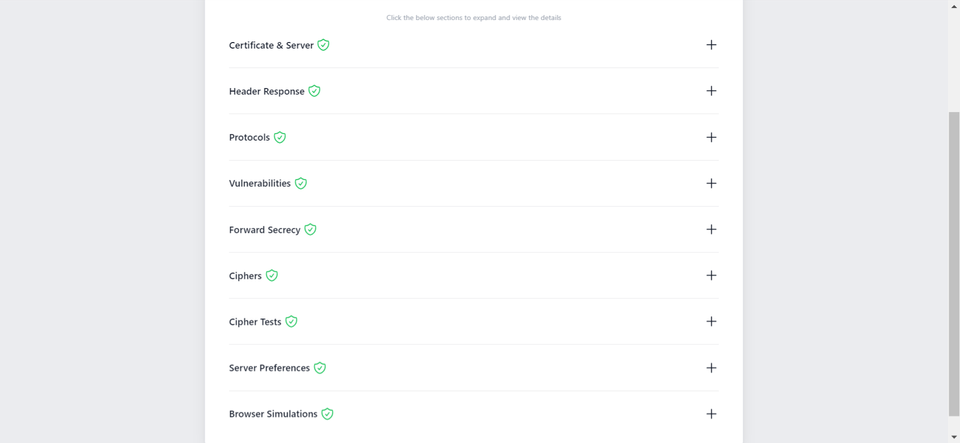
Additionally, you can also performed a detailed check which generates an actionable report with all the ins and out of your SSL Certificate. This includes Protocols, Ciphers, Vulnerabilities and much more.
-
You might require assistance from your web developer or make the necessary updates to your website personally to ensure that all files utilize "https://" and all links leading to and within your website employ "https://".
Discussions and Comments
Click here to view and join in on any discussions and comments on this article.





